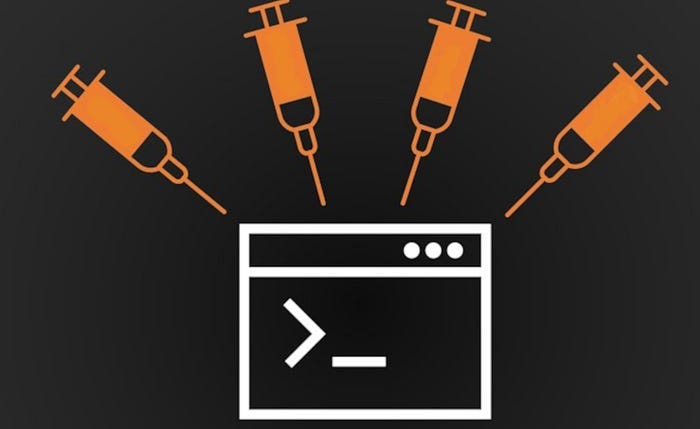
What is OS command injection, and how to prevent it?

In this section, we explain what OS command injection is, and describe how vulnerabilities can be detected and exploited. We also show you some useful

Command injection in Python: examples and prevention
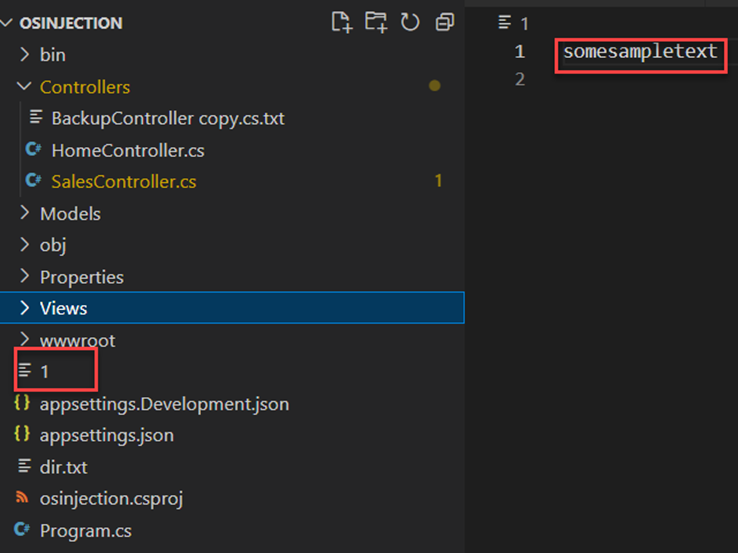
Patching .NET OS Command Injection Vulnerabilities - Site24x7

Command Injection: How it Works and 5 Ways to Protect Yourself

Risk Management Assessment and Control - Risk Management Assessment and Control Managing Risk - Studocu

PCI Secure Coding Training Requirements - PCI DSS GUIDE

What Is Command Injection?, Examples, Methods & Prevention

What is the command injection vulnerability?

What Is an SQL Injection? Cheatsheet and Examples
Blind OS Command Injection via Activation Request!!, by theUnixe

Mandar Parab on LinkedIn: Successfully completed the Ethical Hacking training from Internshala…
Preventing SQL Injection Attacks With Python – Real Python


/i.s3.glbimg.com/v1/AUTH_08fbf48bc0524877943fe86e43087e7a/internal_photos/bs/2020/X/D/vlVfdUTw6uweSYjTWBOw/sem-titulo-2.jpg)